So, you’re wondering about these continuous integration servers that churn out automated builds every few minutes. It’s a pretty common setup these days, and the core idea is simple: catch problems early and often. We’re talking about a system that takes code changes, puts them through a series of automated checks, and gives developers feedback almost instantly. It’s less about magic and more about a disciplined approach to software development.
What’s the Point of Frequent Automated Builds?
Think of it like a rapid fire feedback loop. Instead of waiting days or weeks for a build to happen, only to discover a bunch of issues that are hard to untangle, you’re getting that information within minutes of someone pushing a code change. This means developers can identify and fix mistakes while the context is still fresh in their minds. It drastically reduces the time it takes to get features out the door and keeps the codebase in a more stable, working state.
Early Bug Detection: The Real MVP
The most obvious benefit is catching bugs, and doing it right after they’re introduced. When a developer commits a change, the CI server kicks off a build and runs tests. If something breaks, the build fails, and that developer gets a notification immediately. They know exactly which change likely caused the issue, making it much easier and faster to resolve. This proactive approach prevents minor issues from snowballing into major problems that can derail a whole project.
The Domino Effect of Delayed Feedback
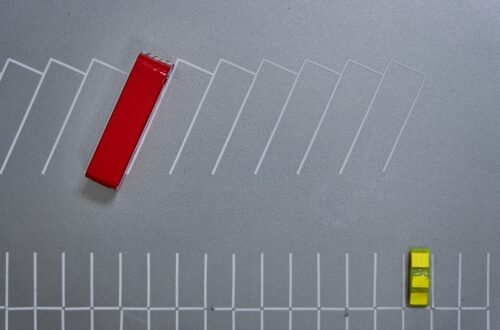
Imagine a team working for a week, with several developers making changes. If the build and testing process is slow, they might not find out about a conflict or a breaking change until much later. This means they might have to redo work, or spend significant time figuring out which of many changes caused the problem. Frequent builds cut through that, showing you the ripples of your changes almost instantaneously.
Maintaining Code Stability
Beyond individual bugs, these frequent automated builds help maintain the overall health and stability of the codebase. By constantly integrating and testing, you’re ensuring that new code plays nicely with existing code. This prevents those dreaded “integration hell” scenarios where merging different branches becomes a monumental task.
The “Always Green” Ideal
Most teams strive for what’s often called an “always green” build. This isn’t some utopian ideal, but a practical goal: the main branch of code should always be in a deployable state. Frequent automated builds and rigorous testing are the bedrock of achieving this. It means you can be reasonably confident that the code you’re about to deploy to production is stable.
How Does This “Every Few Minutes” Thing Actually Work?
The magic, if you can call it that, lies in a combination of tools and a specific workflow. It’s not just about having a fast computer; it’s about setting up a system that’s designed for speed and efficiency. This usually involves a dedicated server or a cloud-based service that’s constantly monitoring your code repository.
Triggering the Build: The Code Commit Event
The primary trigger for these frequent builds is a code commit. When a developer pushes their changes to a shared repository (like Git), that action signals to the CI server that there’s new code to process. The server then pulls down the latest changes and begins its automated sequence.
Webhooks and Polling: The Two Main Approaches
There are generally two ways the CI server knows about new commits. The more efficient method is using webhooks. When a commit is pushed, the repository hosting service (e.g., GitHub, GitLab, Bitbucket) sends a signal (a webhook) directly to the CI server, telling it to start a build. This is near real-time. The older, less efficient way is polling, where the CI server periodically checks the repository for new commits. This can introduce a slight delay and puts more load on both systems.
The Build Pipeline: A Series of Automated Steps
Once the build is triggered, it doesn’t just magically compile. It goes through a defined sequence of steps, often referred to as a “pipeline.”
Compilation and Static Analysis
The first step is usually compiling the code. If it’s a compiled language like Java or C++, the code needs to be turned into executable binaries. At this stage, many CI servers also run static analysis tools. These tools examine the code without executing it, looking for potential code quality issues, stylistic inconsistencies, and even potential security vulnerabilities. This is another layer of early error detection.
Automated Testing: The Backbone of Reliability
After compilation, the heart of the CI process is automated testing. This is where the code’s functionality is verified programmatically.
Unit Tests
These are the most granular tests, focusing on individual functions, methods, or classes. They ensure that small pieces of code behave as expected in isolation. High unit test coverage is crucial for a robust CI system, as they provide the quickest feedback on specific code changes.
Integration Tests
Once individual components are tested, integration tests check how different parts of the system work together. This is important because code that works perfectly in isolation might cause issues when combined with other modules.
End-to-End (E2E) Tests
These are the most comprehensive tests, simulating a real user’s interaction with the application from start to finish. They verify that the entire system, from the user interface down to the database, functions correctly. E2E tests are often the longest-running but provide the highest confidence in the overall application.
Packaging and Deployment Artifacts
If all the tests pass, the CI server often packages the application into a deployable artifact. This could be a Docker image, an executable file, a JAR file, or whatever format is appropriate for the project. This artifact is then stored, ready for potential deployment.
What Tools Make This Happen?
There’s a whole ecosystem of tools designed to facilitate continuous integration. You don’t need to invent this from scratch; you can leverage established solutions.
The Big Players: Jenkins and Its Competitors
Jenkins has been a long-standing champion in the CI/CD space. It’s open-source, highly customizable, and has a massive plugin ecosystem that allows it to integrate with almost any tool or service imaginable. However, it can also be complex to manage and keep secure. For instance, critical vulnerabilities like CVE-2026-33001, discovered recently, highlight the need for diligent security practices and regular updates for Jenkins, as RCE attacks via symbolic links in archives are a serious threat to CI/CD infrastructure.
Managed CI/CD Services
Beyond self-hosted solutions like Jenkins, there are many cloud-based CI/CD platforms. Services like Semaphore, GitHub Actions, GitLab CI/CD, CircleCI, and Travis CI offer managed infrastructure, often simplifying setup and maintenance. These services are increasingly incorporating advanced features. For example, Semaphore’s Agentic CI/CD initiative (with a 2026 focus) aims to integrate AI for more reliable execution and faster workflows, alongside features like Unified Storage which can significantly speed up multi-job tests through improved cache performance.
Infrastructure as Code (IaC) and CI/CD
The trend is increasingly towards integrating Infrastructure as Code (IaC) with CI/CD. Tools like Terraform or Ansible are used to define and manage infrastructure. With IaC, your CI/CD pipeline can not only build and test code but also provision and configure the environments where that code will run. This ensures that the testing environment mirrors production, reducing “it worked on my machine” issues.
GitOps for Deployment
Closely related is GitOps, where Git becomes the single source of truth for declarative infrastructure and application deployment. Changes to the desired state are made in Git, and automated processes ensure that the live environment matches. This is a key enterprise trend for 2026, fitting perfectly with the continuous integration model.
Challenges and Considerations
While the benefits are clear, running frequent automated builds isn’t a set-it-and-forget-it affair. There are practical aspects to consider to ensure the system is effective and sustainable.
Infrastructure Demands: Speed and Scalability
Running builds and tests every few minutes, especially for large projects with extensive test suites, requires significant computational resources. You need build agents that are fast and numerous enough to handle the load, especially if you’re running parallel pipelines. This is where scalable cloud-based solutions or well-maintained on-premises infrastructure becomes crucial. For enterprise environments, scalable parallel pipelines are a must-have feature.
Keeping Test Suites Fast
The “few minutes” target is only achievable if the test suite itself is fast. This often means optimizing tests, running them in parallel where possible, and judiciously choosing which tests run on every commit versus those that run less frequently (e.g., nightly builds). The goal is to get meaningful feedback as quickly as possible.
Maintenance and Monitoring
Your CI/CD server and its associated infrastructure need to be maintained. This includes updating software, managing build agents, and ensuring the system is healthy and performing optimally.
Security: A Constant Battle
With the increasing sophistication of cyber threats, securing your CI/CD pipeline is paramount. As highlighted by Jenkins’ critical vulnerabilities (March 18, 2026), RCE attacks via symbolic links are a tangible risk that can completely compromise your build system. This means staying up-to-date with security patches, carefully managing access, and understanding the attack vectors. The broader software supply chain security shift predicted for 2026 emphasizes moving towards continuous verification of dependencies and real-time monitoring, rather than just periodic scans.
Dependency Management and SBOMs
A key aspect of supply chain security is understanding and verifying all the dependencies your software relies on. This is where Software Bills of Materials (SBOMs) become increasingly important. They provide a clear list of components, giving you visibility into potential vulnerabilities or licensing issues. Integrating SBOM generation and verification into your CI pipeline is becoming a standard practice for enterprise CI/CD in 2026.
Team Culture and Adoption
The most advanced CI/CD system won’t work if the development team doesn’t embrace it. It requires a cultural shift towards shared responsibility for code quality and a commitment to addressing build failures promptly.
Developer Enablement
Developers need to understand how the CI system works, what the tests are doing, and how to interpret the results. Providing clear dashboards, informative build logs, and training can help with adoption.
Feedback on Build Failures
When a build fails, it’s crucial that the feedback is actionable and that there’s a clear process for addressing it. Ignoring failing builds undermines the entire purpose of CI.
The Future: AI and Continuous Verification
The world of CI/CD isn’t static. We’re seeing ongoing innovation, with a strong push towards more intelligence and security integrated into the process.
AI-Assisted CI/CD
AI is starting to play a bigger role. As mentioned, Semaphore’s agentic CI/CD aims to use AI to make workflows more reliable and efficient. This could involve AI helping to intelligently select which tests to run based on code changes, predict potential failure points, or even auto-generate test cases. The trend for enterprise CI/CD in 2026 also includes using AI for SLO (Service Level Objective) tracking, helping to ensure that performance targets are met.
Enhanced Observability
The shift towards continuous verification also implies better observability within the CI/CD process itself. This means having deep insights into how builds are running, where bottlenecks exist, and what the overall health of the pipeline is, allowing for proactive adjustments.
Proactive Security and Intelligent Automation
The push towards continuous verification in the software supply chain means that security checks will be more deeply integrated, not just as a final step, but as an ongoing process throughout the development lifecycle. This isn’t just about scanning for vulnerabilities but also about continuously verifying the integrity of your build artifacts and dependencies. The goal is to move away from reactive security to a more proactive, built-in approach.
The idea of continuous integration servers running automated builds every few minutes is more than just a technical setup; it’s a fundamental shift in how software is developed and maintained. It’s about building quality in from the start, rather than trying to bolt it on at the end.
FAQs
What is a continuous integration server?
A continuous integration server is a tool that automates the process of integrating code changes from multiple developers into a shared repository. It runs automated builds and tests to ensure that the code is functioning correctly.
How often do continuous integration servers run automated builds?
Continuous integration servers typically run automated builds every few minutes, depending on the specific configuration and needs of the development team. This frequent integration helps to catch and fix issues early in the development process.
What are the benefits of running automated builds with continuous integration servers?
Running automated builds with continuous integration servers helps to identify and address integration issues, bugs, and conflicts in the codebase early in the development cycle. This leads to improved code quality, faster feedback for developers, and a more stable and reliable software product.
What types of tests are typically run during automated builds on continuous integration servers?
Automated builds on continuous integration servers often include running unit tests, integration tests, and other types of automated tests to verify the functionality and performance of the code changes. This helps to ensure that the code meets the required quality standards.
What are some popular continuous integration servers used in the industry?
Some popular continuous integration servers used in the industry include Jenkins, Travis CI, CircleCI, TeamCity, and GitLab CI. These tools offer a range of features for automating builds, running tests, and integrating code changes in software development projects.